Token ring local area network (LAN) technology is a communications protocol for local area networks. It uses a special three-byte frame called a "token" that travels around a logical "ring" of workstations or servers. This token passing is a channel access method providing fair access for all stations, and eliminating the collisions of contention-based access methods.
Introduced by IBM in 1984, it was then standardized with protocol IEEE 802.5 and was fairly successful, particularly in corporate environments, but gradually eclipsed by the later versions of Ethernet.
(The main focus of this article is the IBM/IEEE 802.5 version, but there were several other earlier implementations of token rings).
History
A wide range of different local area network technologies were developed in the early 1970s, of which one, the Cambridge Ring had demonstrated the potential of a token passing ring topology.
At the IBM Zurich Research Laboratory Werner Bux and Hans Müller in particular worked on the design and development of IBM's token ring technology.
Early work at MIT led to the 1981, Proteon 10 Mbit/s ProNet-10 token ring network.
In 1981, workstation vendor Apollo Computer introduced their proprietary 12 Mbit/s Apollo token ring (ATR) network running over 75 ohm RG-6U coaxial cabling.
On October 15 1985, IBM launched their own proprietary IBM Token Ring products. It ran at 4 Mbit/s, and attachment was possible from IBM PCs, midrange computers and mainframes. It used a convenient star-wired physical topology, and ran over shielded twisted-pair cabling - and shortly became the basis for the (ANSI)/IEEE standard 802.5.
In 1988 the faster 16 Mbit/s token ring was standardized by the 802.5 working group.
During this time, IBM argued strongly that token ring LANs were superior to Ethernet, especially under load, but these claims were fiercely debated.
Although an increase to 100 Mbit/s was standardized and marketed during the wane of token ring's existence, it was never widely used, ("IBM does not view high-speed token ring as a requirement for the majority of its customers, and therefore the decision has been made not to provide 100 Mbps high-speed token ring uplinks on its products..."), and while a 1000 Mbit/s was approved in 2001, no products were ever brought to market, and standards activity came to a standstill as Fast Ethernet and Gigabit Ethernet dominated the local area networking market.
100 Mbit/s IBM Token Ring Management Adapter with Wake On LAN. Both UTP (RJ45) and STP (IBM Data Connector) interfaces are present.
Token Ring Network Interface Cards (NICs) with varying interfaces from: ISA, PCI and MicroChannel
Madge 4/16Mbit/s TokenRing ISA NIC
Comparison with Ethernet
Ethernet and Token ring have some notable differences:
- Token Ring access is more deterministic, compared to Ethernet's contention-based CSMA/CD
- Ethernet supports a direct cable connection between two network interface cards by the use of a crossover cable or through auto-sensing if supported. Token ring does not inherently support this feature and requires additional software and hardware to operate on a direct cable connection setup.
- Token ring eliminates collision by the use of a single-use token and early token release to alleviate the down time. Ethernet alleviates collision by carrier sense multiple access and by the use of an intelligent switch; primitive Ethernet devices like hubs can agitate a collision due to repeating traffic blindly.
- Token ring network interface cards contain all of the intelligence required for speed autodetection, routing and can drive themselves on many MAUs that operate without power (most MAUs operate in this fashion, with only requiring a power supply for LEDs). Ethernet network interface cards can theoretically operate on a passive hub to a degree, but not as a large LAN and the issue of collisions is still present.
- Token ring employs 'access priority' in which certain nodes can have priority over the token. Unswitched Ethernet does not have provisioning for an access priority system as all nodes have equal contest for traffic.
- Multiple identical MAC addresses are supported on token ring (a feature used by S/390 mainframes). Switched Ethernet cannot support duplicate MAC addresses without reprimand.
- Token Ring was more complex than Ethernet, requiring a specialized processor and licensed MAC/LLC firmware for each interface. By contrast, Ethernet included both the (simpler) firmware and the lower licensing cost in the MAC chip. Interface parts cost (using a Texas Instruments TMS380C16 MAC and PHY) were approximately three times that of an Ethernet interface using the Intel 82586 MAC and PHY.
- Initially both networks used expensive cable, but once unshielded twisted pair (CAT3 cable) was standardized for Ethernet with 10-BASE-T and 100-BASE-T, sales of it increased markedly it had a distinct advantage.
Operation
Stations on a token ring LAN are logically organized in a ring topology with data being transmitted sequentially from one ring station to the next with a control token circulating around the ring controlling access. Similar token passing mechanisms are used by ARCNET, token bus, 100VG-AnyLAN (802.12) and FDDI, and they have theoretical advantages over the CSMA/CD of early Ethernet.
A token ring network can be modelled as a polling system where a single server provides service to queues in a cyclic order.
Access control
The data transmission process goes as follows:
- Empty information frames are continuously circulated on the ring.
- When a computer has a message to send, it seizes the token. The computer will then be able to send the frame.
- The frame is then examined by each successive workstation. The workstation that identifies itself to be the destination for the message copies it from the frame and changes the token back to 0.
- When the frame gets back to the originator, it sees that the token has been changed to 0 and that the message has been copied and received. It removes the message from the frame.
- The frame continues to circulate as an "empty" frame, ready to be taken by a workstation when it has a message to send.
Multistation Access Units and Controlled Access Units
Main article: Media Access Unit
The IBM 8228 Multistation Access Unit with accompanying Setup Aid to prime the relays on each port
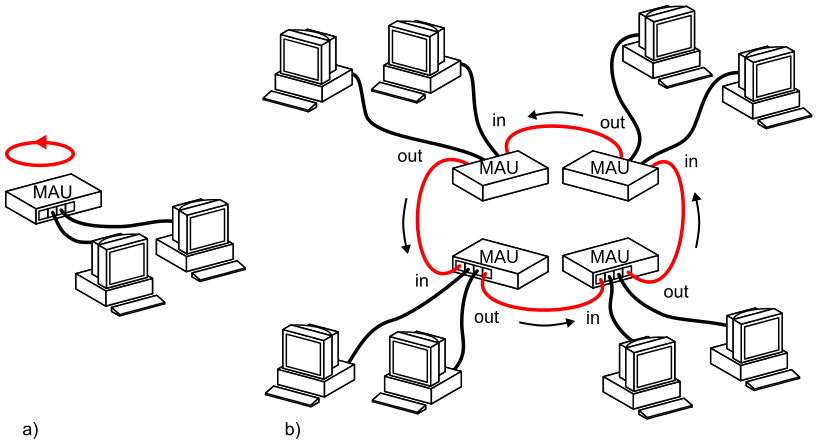
Physically, a token ring network is wired as a star, with 'MAUs' in the center, 'arms' out to each station, and the loop going out-and-back through each.
A MAU could present in the form of a hub or a switch; since token ring had no collisions many MAUs were manufactured as hubs. Although Token Ring runs on LLC, it includes Source Routing to forward packets beyond the local network. The majority of MAUs are configured in a 'concentration' configuration by default, but later MAUs also supporting a feature to act as splitters and not concentrators exclusively such as on the IBM 8226.
Later IBM would release Controlled Access Units that could support multiple MAU modules known as a Lobe Attachment Module. The CAUs supported features such as Dual-Ring Redundancy for alternate routing in the event of a dead port, modular concentration with LAMs, and multiple interfaces like most later MAUs. This offered a more reliable setup and remote management than with an unmanaged MAU hub.
Cabling and interfaces
Cabling is generally IBM "Type-1", a heavy two-pair 150 Ohm shielded twisted pair cable. This was the basic cable for the "IBM Cabling System", a structured cabling system that IBM hoped would be widely adopted. Unique hermaphroditic connectors, commonly referred to as IBM Data Connectors in formal writing or colloquially as Boy George connectors were used. The connectors have the disadvantage of being quite bulky, requiring at least 3 x 3 cm panel space, and being relatively fragile. The advantages of the connectors being that they are genderless and have superior shielding over standard unshielded RJ45. Connectors at the computer were usually DE-9 female.
In later implementations of Token Ring, Cat 6 cabling was also supported, so RJ45 connectors were used on both of the MAUs, CAUs and NICs; with many of the network cards supporting both RJ45 and DE-9 for backwards compatibility.