Temporal Key Integrity Protocol or TKIP was a stopgap security protocol used in the IEEE 802.11 wireless networking standard. TKIP was designed by the IEEE 802.11i task group and the Wi-Fi Alliance as an interim solution to replace WEP without requiring the replacement of legacy hardware. This was necessary because the breaking of WEP had left WiFi networks without viable link-layer security, and a solution was required for already deployed hardware. TKIP is no longer considered secure and was deprecated in the 2012 revision of the 802.11 standard.
Background
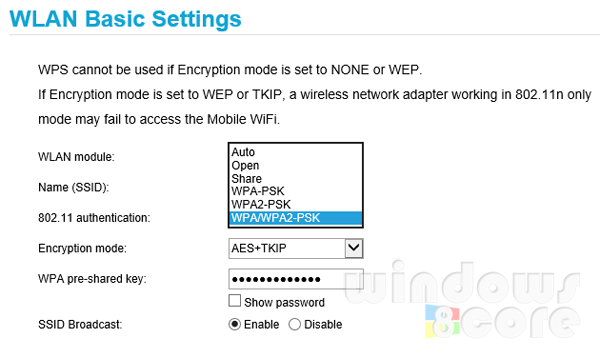
On October 31, 2002, the Wi-Fi Alliance endorsed TKIP under the name Wi-Fi Protected Access (WPA). The IEEE endorsed the final version of TKIP, along with more robust solutions such as 802.1X and the AES based CCMP, when they published IEEE 802.11i-2004 on 23 July 2004. The Wi-Fi Alliance soon afterwards adopted the full specification under the marketing name WPA2.
TKIP was deprecated by the IEEE in January 2009.
Technical details
TKIP and the related WPA standard implement three new security features to address security problems encountered in WEP protected networks. First, TKIP implements a key mixing function that combines the secret root key with the initialization vector before passing it to the RC4 initialization. WEP, in comparison, merely concatenated the initialization vector to the root key, and passed this value to the RC4 routine. This permitted the vast majority of the RC4 based WEP related key attacks. Second, WPA implements a sequence counter to protect against replay attacks. Packets received out of order will be rejected by the access point. Finally, TKIP implements a 64-bit Message Integrity Check (MIC).
To be able to run on legacy WEP hardware with minor upgrades, TKIP uses RC4 as its cipher. TKIP also provides a rekeying mechanism. TKIP ensures that every data packet is sent with a unique encryption key.
Key mixing increases the complexity of decoding the keys by giving an attacker substantially less data that has been encrypted using any one key. WPA2 also implements a new message integrity code, MIC. The message integrity check prevents forged packets from being accepted. Under WEP it was possible to alter a packet whose content was known even if it had not been decrypted.
Security
TKIP uses the same underlying mechanism as WEP, and consequently is vulnerable to a number of similar attacks. The message integrity check, per-packet key hashing, broadcast key rotation, and a sequence counter discourage many attacks. The key mixing function also eliminates the WEP key recovery attacks.
Notwithstanding these changes, the weakness of some of these additions have allowed for new, although narrower, attacks.
Packet Spoofing and Decryption
TKIP is vulnerable to a MIC key recovery attack that, if successfully executed, permits an attacker to transmit and decrypt arbitrary packets on the network being attacked. The current publicly available TKIP-specific attacks do not reveal the Pairwise Master Key or the Pairwise Temporal Keys. On November 8, 2008, Martin Beck and Erik Tews released a paper detailing how to recover the MIC key and transmit a few packets. This attack was improved by Mathy Vanhoef and Frank Piessens in 2013, where they increase the amount of packets an attacker can transmit, and show how an attacker can also decrypt arbitrary packets.
The basis of the attack is an extension of the WEP chop-chop attack. Because WEP uses a cryptographically insecure checksum mechanism (CRC32), an attacker can guess individual bytes of a packet, and the wireless access point will confirm or deny whether or not the guess is correct. If the guess is correct, the attacker will be able to detect the guess is correct and continue to guess other bytes of the packet. However, unlike the chop-chop attack against a WEP network, the attacker must wait for at least 60 seconds after an incorrect guess (a successful circumvention of the CRC32 mechanism) before continuing the attack. This is because although TKIP continues to use the CRC32 checksum mechanism, it implements an additional MIC code named Michael. If two incorrect Michael MIC codes are received within 60 seconds, the access point will implement countermeasures, meaning it will rekey the TKIP session key, thus changing future keystreams. Accordingly, attacks on TKIP will wait an appropriate amount of time to avoid these countermeasures. Because ARP packets are easily identified by their size, and the vast majority of the contents of this packet would be known to an attacker, the number of bytes an attacker must guess using the above method is rather small (approximately 14 bytes). Beck and Tews estimate recovery of 12 bytes is possible in about 12 minutes on a typical network, which would allow an attacker to transmit 3–7 packets of at most 28 bytes. Vanhoef and Piessens improved this technique by relying on fragmentation, allowing an attacker to transmit arbitrary many packets, each at most 112 bytes in size. The Vanhoef-Piessens attacks also can be used to decrypt arbitrary packets of the attack's choice.
An attacker already has access to the entire ciphertext packet. Upon retrieving the entire plaintext of the same packet, the attacker has access to the keystream of the packet, as well as the MIC code of the session. Using this information the attacker can construct a new packet and transmit it on the network. To circumvent the WPA implemented replay protection, the attacks use QoS channels to transmit these newly constructed packets. An attacker able to transmit these packets may be able to implement any number of attacks, including ARP poisoning attacks, denial of service, and other similar attacks, with no need of being associated with the network.
Royal Holloway attack
A group of security researchers at the Information Security Group at Royal Holloway, University of London reported a theoretical attack on TKIP which exploits the underlying RC4 encryption mechanism. TKIP uses a similar key structure to WEP with the low 16-bit value of a sequence counter (used to prevent replay attacks) being expanded into the 24-bit "IV", and this sequence counter always increment on every new packet. An attacker can use this key structure to improve existing attacks on RC4. In particular, if the same data is encrypted multiple times, an attacker can learn this information from only 224 connections. While they claim that this attack is on the verge of practicality, only simulations were performed, and the attack has not been demonstrated in practice.
Legacy
ZDNet reported on June 18, 2010 that WEP & TKIP would soon be disallowed on Wi-Fi devices by the Wi-Fi alliance. However, a survey in 2013 showed that it was still in widespread use.