Ping is a computer network administration software utility used to test the reachability of a host on an Internet Protocol (IP) network and to measure the round-trip time for messages sent from the originating host to a destination computer and back. The name comes from active sonar terminology that sends a pulse of sound and listens for the echo to detect objects underwater; however, the acronym "PING" meaning "Packet InterNet Groper" has been in use since early days in computing for testing and measuring networks and the Internet.
Ping operates by sending Internet Control Message Protocol (ICMP) echo request packets to the target host and waiting for an ICMP echo reply. It measures the round-trip time from transmission to reception, reporting errors and packet loss. The results of the test usually include a statistical summary of the response packets received, including the minimum, maximum, the mean round-trip times, and usually standard deviation of the mean.
The command-line options for the ping utility and its output vary depending on implementation. Options may include the size of the payload, count of tests, and limits for the number of hops (TTL) that probes traverse. Many systems provide a companion utility ping6, for similar testing on Internet Protocol version 6 (IPv6) networks.
History
The ping utility was written by Mike Muuss in December 1983 as a tool to troubleshoot problems in an IP network. He was inspired by a remark by David Mills on using ICMP echo packets for IP network diagnosis and measurements. The author named it after the sound that sonar makes, since its methodology is similar to sonar's echo location.
RFC 1122 prescribes that any host must process an echo-request and issue an echo-reply in return.
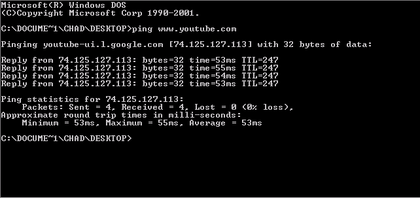
Sample ping test
The following is the output of running ping under Linux for sending five probes to the target host www.example.com:
$ ping -c 5 www.example.com PING www.example.com (93.184.216.119): 56 data bytes 64 bytes from 93.184.216.119: icmp_seq=0 ttl=56 time=11.632 ms 64 bytes from 93.184.216.119: icmp_seq=1 ttl=56 time=11.726 ms 64 bytes from 93.184.216.119: icmp_seq=2 ttl=56 time=10.683 ms 64 bytes from 93.184.216.119: icmp_seq=3 ttl=56 time=9.674 ms 64 bytes from 93.184.216.119: icmp_seq=4 ttl=56 time=11.127 ms --- www.example.com ping statistics --- 5 packets transmitted, 5 packets received, 0.0% packet loss round-trip min/avg/max/stddev = 9.674/10.968/11.726/0.748 ms
The utility summarizes its results after completing the ping probes. The shortest round trip time was 9.674 ms, the average was 10.968 ms, and the maximum value was 11.726 ms. The measurement had a standard deviation of 0.748 ms.
Error indications
In cases of no response from the target host, most implementations of ping display nothing, or periodically print notifications about timing out. Possible ping outputs indicating a problem include the following:
- H, !N or !P – host, network or protocol unreachable
- S – source route failed
- F – fragmentation needed
- U or !W – destination network/host unknown
- I – source host is isolated
- A – communication with destination network administratively prohibited
- Z – communication with destination host administratively prohibited
- Q – for this ToS the destination network is unreachable
- T – for this ToS the destination host is unreachable
- X – communication administratively prohibited
- V – host precedence violation
- C – precedence cutoff in effect
In case of error, the target host or an intermediate router sends back an ICMP error message, for example "host unreachable" or "TTL exceeded in transit". In addition, these messages include the first eight bytes of the original message (in this case header of the ICMP echo request, including the quench value), so the ping utility can match responses to originating queries.
Message format
ICMP packet
IP Datagram
| Bits 0–7 | Bits 8–15 | Bits 16–23 | Bits 24–31 | |
|---|---|---|---|---|
| IP Header (20 bytes) | Version/IHL | Type of service | Length | |
| Identification | flags and offset | |||
| Time To Live (TTL) | Protocol | Checksum | ||
| Source IP address | ||||
| Destination IP address | ||||
| ICMP Header (8 bytes) | Type of message | Code | Checksum | |
| Header Data | ||||
| ICMP Payload (optional) | Payload Data |
Generic composition of an ICMP 32-byte packet:
- IP Header (in blue): protocol set to 1 (ICMP) and Type of Service set to 0.
- ICMP Header (in red):
- Type of ICMP message (8 bits)
- Code (8 bits)
- Checksum (16 bits), calculated with the ICMP part of the packet (the IP header is not used). It is the 16-bit one's complement of the one's complement sum of the ICMP message starting with the Type field[8]
- Header Data (32 bits) field, which in this case (ICMP echo request and replies), will be composed of identifier (16 bits) and sequence number (16 bits).
- ICMP Payload: payload for the different kind of answers; can be an arbitrary length, left to implementation detail. However, the packet including IP and ICMP headers must be less than the maximum transmission unit of the network or risk being fragmented.
Echo request
The echo request ("ping") is an ICMP message.
| 00 | 01 | 02 | 03 | 04 | 05 | 06 | 07 | 08 | 09 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 | 21 | 22 | 23 | 24 | 25 | 26 | 27 | 28 | 29 | 30 | 31 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Type = 8 | Code = 0 | Header Checksum | |||||||||||||||||||||||||||||
| Identifier | Sequence Number | ||||||||||||||||||||||||||||||
| Payload |
The Identifier and Sequence Number can be used by the client to match the reply with the request that caused the reply. In practice, most Linux systems use a unique identifier for every ping process, and sequence number is an increasing number within that process. Windows uses a fixed identifier, which varies between Windows versions, and a sequence number that is only reset at boot time.
Echo reply
The echo reply is an ICMP message generated in response to an echo request; it is mandatory for all hosts and routers, and must include the exact payload received in the request.
| 00 | 01 | 02 | 03 | 04 | 05 | 06 | 07 | 08 | 09 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 | 21 | 22 | 23 | 24 | 25 | 26 | 27 | 28 | 29 | 30 | 31 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Type = 0 | Code = 0 | Header Checksum | |||||||||||||||||||||||||||||
| Identifier | Sequence Number | ||||||||||||||||||||||||||||||
| Payload |
- Type and code must be set to 0.
- The identifier and sequence number can be used by the client to determine which echo requests are associated with the echo replies.
Payload
The payload of the packet is generally filled with ASCII characters, as the output of the tcpdump utility shows:
16:24:47.966461 IP (tos 0x0, ttl 128, id 15103, offset 0, flags [none], proto: ICMP (1), length: 60) 192.168.146.22 > 192.168.144.5: ICMP echo request, id 1, seq 38, length 40 0x0000: 4500 003c 3aff 0000 8001 5c55 c0a8 9216 E..<:.....\U.... 0x0010: c0a8 9005 0800 4d35 0001 0026 6162 6364 ......M5...&abcd 0x0020: 6566 6768 696a 6b6c 6d6e 6f70 7172 7374 efghijklmnopqrst 0x0030: 7576 7761 6263 6465 6667 6869 uvwabcdefghi
The payload includes a timestamp of when the message was sent and a sequence number. This allows ping to compute the round trip time in a stateless manner without needing to record when packets were sent.
Security considerations
The flood ping option exists of many implementations, sending requests as fast as possible in an attempt to determine the response of the network under high-load conditions. That option is restricted to users having administrative privileges, but may be used in denial-of-service attacks to induce a ping flood, in which the attacker attempts to overwhelm the victim with ICMP echo requests.
Ping has been considered as a security risk as merely acknowledging a host's presence turns it into a potential target. For these reasons, many systems provide means to disable the reply, despite the fact that RFC 1122 mandates hosts to always send a reply.
Host discovery, scanning or ping sweep is a feature of network scanning tools such as nmap, working by utilizing ICMP echo packets.