In computing, iSCSI is an acronym for Internet Small Computer System Interface, an Internet Protocol (IP)-based storage networking standard for linking data storage facilities.
By carrying SCSI commands over IP networks, iSCSI is used to facilitate data transfers over intranets and to manage storage over long distances. iSCSI can be used to transmit data over local area networks (LANs), wide area networks (WANs), or the Internet and can enable location-independent data storage and retrieval.
The protocol allows clients (called initiators) to send SCSI commands (CDBs) to SCSI storage devices (targets) on remote servers. It is a storage area network (SAN) protocol, allowing organizations to consolidate storage into data center storage arrays while providing hosts (such as database and web servers) with the illusion of locally attached disks.
Unlike traditional Fibre Channel, which usually requires dedicated cabling, iSCSI can be run over long distances using existing network infrastructure. iSCSI was pioneered by IBM and Cisco in 1998 and submitted as draft standard in March 2000.
Concepts
In essence, iSCSI allows two hosts to negotiate and then exchange SCSI commands using Internet Protocol (IP) networks. By doing this, iSCSI takes a popular high-performance local storage bus and emulates it over a wide range of networks, creating a storage area network (SAN). Unlike some SAN protocols, iSCSI requires no dedicated cabling; it can be run over existing IP infrastructure. As a result, iSCSI is often seen as a low-cost alternative to Fibre Channel, which requires dedicated infrastructure except in its FCoE (Fibre Channel over Ethernet) form. However, the performance of an iSCSI SAN deployment can be severely degraded if not operated on a dedicated network or subnet (LAN or VLAN), due to competition for a fixed amount of bandwidth.
Although iSCSI can communicate with arbitrary types of SCSI devices, system administrators almost always use it to allow server computers (such as database servers) to access disk volumes on storage arrays. iSCSI SANs often have one of two objectives:
Storage consolidationOrganizations move disparate storage resources from servers around their network to central locations, often in data centers; this allows for more efficiency in the allocation of storage, as the storage itself is no longer tied to a particular server. In a SAN environment, a server can be allocated a new disk volume without any changes to hardware or cabling. Disaster recoveryOrganizations mirror storage resources from one data center to a remote data center, which can serve as a hot standby in the event of a prolonged outage. In particular, iSCSI SANs allow entire disk arrays to be migrated across a WAN with minimal configuration changes, in effect making storage "routable" in the same manner as network traffic.
Initiator
Further information: SCSI initiator
An initiator functions as an iSCSI client. An initiator typically serves the same purpose to a computer as a SCSI bus adapter would, except that, instead of physically cabling SCSI devices (like hard drives and tape changers), an iSCSI initiator sends SCSI commands over an IP network. An initiator falls into two broad types:
A software initiator uses code to implement iSCSI. Typically, this happens in a kernel-resident device driver that uses the existing network card (NIC) and network stack to emulate SCSI devices for a computer by speaking the iSCSI protocol. Software initiators are available for most popular operating systems and are the most common method of deploying iSCSI.
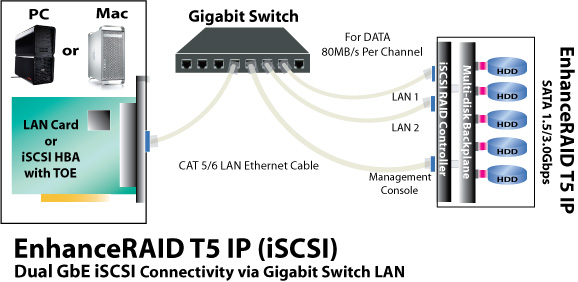
A hardware initiator uses dedicated hardware, typically in combination with firmware running on that hardware, to implement iSCSI. A hardware initiator mitigates the overhead of iSCSI and TCP processing and Ethernet interrupts, and therefore may improve the performance of servers that use iSCSI. An iSCSI host bus adapter (more commonly, HBA) implements a hardware initiator. A typical HBA is packaged as a combination of a Gigabit (or 10 Gigabit) Ethernet network interface controller, some kind of TCP/IP offload engine (TOE) technology and a SCSI bus adapter, which is how it appears to the operating system. An iSCSI HBA can include PCI option ROM to allow booting from an iSCSI SAN.
An iSCSI offload engine, or iSOE card, offers an alternative to a full iSCSI HBA. An iSOE "offloads" the iSCSI initiator operations for this particular network interface from the host processor, freeing up CPU cycles for the main host applications. iSCSI HBAs or iSOEs are used when the additional performance enhancement justifies the additional expense of using an HBA for iSCSI, rather than using a software-based iSCSI client (initiator). iSOE may be implemented with additional services such as TCP offload engine (TOE) to further reduce host server CPU usage.
Target
See also: SCSI target
The iSCSI specification refers to a storage resource located on an iSCSI server (more generally, one of potentially many instances of iSCSI storage nodes running on that server) as a target.
"iSCSI target" should not be confused with the term "iSCSI" as the latter is a protocol and not a storage server instance.
An iSCSI target is often a dedicated network-connected hard disk storage device, but may also be a general-purpose computer, since as with initiators, software to provide an iSCSI target is available for most mainstream operating systems.
Common deployment scenarios for an iSCSI target include:
Storage array
In a data center or enterprise environment, an iSCSI target often resides in a large storage array. These arrays can be in the form of commodity hardware with free-software-based iSCSI implementations, or as commercial products such as in StorTrends, Pure Storage, HP StorageWorks, EqualLogic, Tegile Systems, Nimble storage, Reduxio, IBM Storwize family, Isilon, NetApp filer, EMC Corporation NS-series, CX4, VNX, VNXe, VMAX, Hitachi Data Systems HNAS, or Pivot3 vSTAC.
A storage array usually provides distinct iSCSI targets for numerous clients.
Software target
See also: List of SAN network management systems
Nearly all modern mainstream server operating systems (such as BSD, Linux, Solaris or Windows Server) can provide iSCSI target functionality, either as a built-in feature or with supplemental software. Some specific-purpose operating systems (such as FreeNAS, NAS4Free, Openfiler, OpenMediaVault, or based on OpenSolaris and derivatives like napp-it, NexentaStor, OmniOS and OpenIndiana) implement iSCSI target support.
Logical unit number
Main article: Logical unit number
In SCSI terminology, LUN stands for logical unit number. A LUN represents an individually addressable (logical) SCSI device that is part of a physical SCSI device (target). In an iSCSI environment, LUNs are essentially numbered disk drives. An initiator negotiates with a target to establish connectivity to a LUN; the result is an iSCSI connection that emulates a connection to a SCSI hard disk. Initiators treat iSCSI LUNs the same way as they would a raw SCSI or IDE hard drive; for instance, rather than mounting remote directories as would be done in NFS or CIFS environments, iSCSI systems format and directly manage filesystems on iSCSI LUNs.
In enterprise deployments, LUNs usually represent subsets of large RAID disk arrays, often allocated one per client. iSCSI imposes no rules or restrictions on multiple computers sharing individual LUNs; it leaves shared access to a single underlying filesystem as a task for the operating system.
Network booting
For general data storage on an already-booted computer, any type of generic network interface may be used to access iSCSI devices. However, a generic consumer-grade network interface is not able to boot a diskless computer from a remote iSCSI data source. Instead, it is commonplace for a server to load its initial operating system from a TFTP server or local boot device, and then use iSCSI for data storage once booting from the local device has finished.
A separate DHCP server may be configured to assist interfaces equipped with network boot capability to be able to boot over iSCSI. In this case, the network interface looks for a DHCP server offering a PXE or bootp boot image, This is used to kick off the iSCSI remote boot process, using the booting network interface's MAC address to direct the computer to the correct iSCSI boot target. One can then use a software-only approach to load a small boot program which can in turn mount a remote iSCSI target as if it was a local SCSI drive and then fire the boot process from said iSCSI target. This can be achieved using an existing Preboot Execution Environment (PXE) boot ROM, which is available on many wired Ethernet adapters. The boot code can also be loaded from CD/DVD, floppy disk (or floppy disk image) and USB storage, or it can replace existing PXE boot code on adapters that can be re-flashed. The most popular free software to offer iSCSI boot support is iPXE.
Most Intel Ethernet controllers for servers support iSCSI boot.
Addressing
iSCSI uses TCP (typically TCP ports 860 and 3260) for the protocols itself, with higher-level names used to address the objects within the protocol. Special names refer to both iSCSI initiators and targets. iSCSI provides three name-formats:
iSCSI Qualified Name (IQN)Format: The iSCSI Qualified Name is documented in RFC 3720, with further examples of names in RFC 3721. Briefly, the fields are:
- literal iqn (iSCSI Qualified Name)
- date (yyyy-mm) that the naming authority took ownership of the domain
- reversed domain name of the authority (e.g. org.alpinelinux, com.example, to.yp.cr)
- Optional ":" prefixing a storage target name specified by the naming authority.
From the RFC:
Naming String defined by Type Date Auth "example.com" naming authority +--++-----+ +---------+ +-----------------------------+ | || | | | | | iqn.1992-01.com.example:storage:diskarrays-sn-a8675309 iqn.1992-01.com.example iqn.1992-01.com.example:storage.tape1.sys1.xyz iqn.1992-01.com.example:storage.disk2.sys1.xyz
Extended Unique Identifier (EUI)Format: eui.{EUI-64 bit address} (e.g. eui.02004567A425678D)T11 Network Address Authority (NAA)Format: naa.{NAA 64 or 128 bit identifier} (e.g. naa.52004567BA64678D)
IQN format addresses occur most commonly. They are qualified by a date (yyyy-mm) because domain names can expire or be acquired by another entity.
The IEEE Registration authority provides EUI in accordance with the EUI-64 standard. NAA is part OUI which is provided by the IEEE Registration Authority. NAA name formats were added to iSCSI in RFC 3980, to provide compatibility with naming conventions used in Fibre Channel and Serial Attached SCSI (SAS) storage technologies.
Usually, an iSCSI participant can be defined by three or four fields:
- Hostname or IP Address (e.g., "iscsi.example.com")
- Port Number (e.g., 3260)
- iSCSI Name (e.g., the IQN "iqn.2003-01.com.ibm:00.fcd0ab21.shark128")
- An optional CHAP Secret (e.g., "secretsarefun")
iSNS
Main article: Internet Storage Name Service
iSCSI initiators can locate appropriate storage resources using the Internet Storage Name Service (iSNS) protocol. In theory, iSNS provides iSCSI SANs with the same management model as dedicated Fibre Channel SANs. In practice, administrators can satisfy many deployment goals for iSCSI without using iSNS.
Security
Authentication
iSCSI initiators and targets prove their identity to each other using CHAP, which includes a mechanism to prevent cleartext passwords from appearing on the wire. By itself, CHAP is vulnerable to dictionary attacks, spoofing, and reflection attacks. If followed carefully, the best practices for using CHAP within iSCSI reduce the surface for these attacks and mitigate the risks.
Additionally, as with all IP-based protocols, IPsec can operate at the network layer. The iSCSI negotiation protocol is designed to accommodate other authentication schemes, though interoperability issues limit their deployment.
Logical network isolation
To ensure that only valid initiators connect to storage arrays, administrators most commonly run iSCSI only over logically isolated backchannel networks. In this deployment architecture, only the management ports of storage arrays are exposed to the general-purpose internal network, and the iSCSI protocol itself is run over dedicated network segments or virtual LANs (VLAN). This mitigates authentication concerns; unauthorized users are not physically provisioned for iSCSI, and thus cannot talk to storage arrays. However, it also creates a transitive trust problem, in that a single compromised host with an iSCSI disk can be used to attack storage resources for other hosts.